Cyber Security in Energy Systems Digitalization for Net Zero transition
Smart grids, which are hastening the green energy transition, present cybersecurity issues.
Since 2006, the rapid increase of renewable energy capacity has been primarily enabled by the digital revolution in clean energy, which depends on disruptive technologies and innovations to integrate various forms of renewable energy into the grid. However, increasing expansion has increased the cybersecurity complexity of wind and solar assets, as well as the overall system.
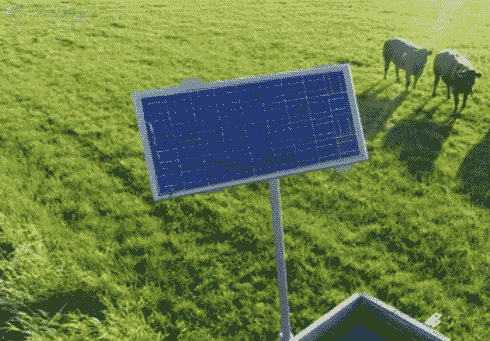
Until recently, traditional grids used a centralized power generating paradigm, with electricity and information moving in just one direction. As more distributed renewable energy sources, such as household solar panels, are adopted and integrated into the grid, a two-way flow of both electricity and information is required. Similarly, smart grids offer bidirectional energy transfer as well as two-way communication and control.
Furthermore, the connection of renewable energy resources to legacy operational technology (OT) opens the door to massive assaults. Renewables are frequently geographically dispersed in remote places and operate with enhanced controls and digital sensors close to generation sources. OT is a component of renewable energy facilities that was not designed to connect to the internet. Connecting these resources to the power grid raises the possibility of scaled assaults that transcend beyond local resources and into bulk energy OT systems.
COLLECTION OF DATA
Data security and privacy issues are exacerbated by sophisticated data harvesting. Traditional grids collect rudimentary data from a small number of data points to measure substantial changes in load or voltage data over time.
Renewable energy cyber threats will become more frequent and severe. Although renewable energy presently accounts for a small percentage of the entire energy sector, it is prepared to bear a disproportionate burden in terms of the frequency and severity of cyberattacks, which will only increase as renewables increase their share of the energy market.
Because most of these linked gadgets are ubiquitous in society, a single cyberattack on a smart grid might have the devastating cascade effect of shutting down the electricity grid. Furthermore, because these devices are largely homogeneous, a single compromised device can swiftly escalate into a widespread disaster.
PROTECTION IN ADVANCE
The green energy transformation must begin with cybersecurity risk considerations, not finish with them. Companies must proactively safeguard their assets, effectively support infrastructure and information capital, and maintain their resistance to cyber-attacks as digital changes continue to spread across the energy ecosystem, fueling the green energy transition. A security-by-design strategy may instill a cyber risk-aversion mentality and establish trust from the start in renewable energy digital transitions.
Renewable energy operating assets are vulnerable to assault due to a lack of visibility. This is especially true when operators are attempting to safeguard dispersed power generating assets located distant from their core location, such as an offshore wind farm. Energy businesses will want to conduct and maintain a complete and ongoing discovery and inventory of operational assets to better understand their present state and related vulnerabilities in order to safeguard these assets.
CYBER SECURITY
To achieve a green energy world, digitally driven change need cybersecurity resilience. Incorporating security-by-design concepts into renewable energy digital transformations and adopting a cybersecurity resilience framework can assist energy organizations in managing a wide range of cyber risks throughout the whole ecosystem. It may also instill trust in digital innovations aimed at hastening the transition to renewables and paving the road for global decarbonisation.
To succeed in a green energy environment, renewable energy firms must grab possibilities from digitally driven change while also protecting themselves from the accompanying dangers in order to retain operational resilience and stakeholder confidence. There is no time to waste as the assault terrain develops tremendously.
Visit our website to know more: https://bit.ly/3V0WLbF
For more information and group participation, contact us: [email protected]
Leadvent Group - Industry Leading Events for Business Leaders!